Server-Side Object Encryption with KES
This procedure assumes you have access to a Kubernetes cluster with an active MinIO Operator installation. For instructions on running KES, see the KES docs.
As part of this procedure, you will:
Use the MinIO Operator Console to create or manage a MinIO Tenant.
Access the Encryption settings for that tenant and configure SSE using a supported Key Management System.
Create a new EK for use with SSE.
Configure automatic bucket-default SSE-KMS.
For production baremetal environments, see the MinIO on Linux documentation for tutorials on configuring MinIO with KES and your KMS.
Important
Enabling SSE on a MinIO deployment automatically encrypts the backend data for that deployment using the default encryption key.
MinIO requires access to KES and the external KMS to decrypt the backend and start normally.
The KMS must maintain and provide access to the MINIO_KMS_KES_KEY_NAME.
You cannot disable KES later or “undo” the SSE configuration at a later point.
Prerequisites
MinIO Kubernetes Operator
Ensure your target Kubernetes cluster has a valid and working installation of the MinIO Kubernetes Operator. This documentation assumes the latest stable Operator, version 5.0.18.
See Deploy the MinIO Operator for complete documentation on deploying the MinIO Operator.
Ensure KES Access to a Supported KMS Target
This procedure assumes an existing supported KMS installation accessible from the Kubernetes cluster.
For deployments within the same Kubernetes cluster as the MinIO Tenant, you can use Kubernetes service names to allow the MinIO Tenant to establish connectivity to the target KMS service.
For deployments external to the Kubernetes cluster, you must ensure the cluster supports routing communications between Kubernetes services and pods and the external network. This may require configuration or deployment of additional Kubernetes network components and/or enabling access to the public internet.
Defer to the documentation for your chosen KMS solution for guidance on deployment and configuration.
Refer to the configuration instruction in the KES documentation for your chosen supported KMS:
Deploy MinIO Tenant with Server-Side Encryption
1) Access the Operator Console
Temporarily forward traffic between the local host machine and the MinIO Operator Console and retrieve the JWT token for your Operator deployment. For instructions, see Configure access to the Operator Console service.
Open your browser to the temporary URL and enter the JWT Token into the login page. You should see the Tenants page:
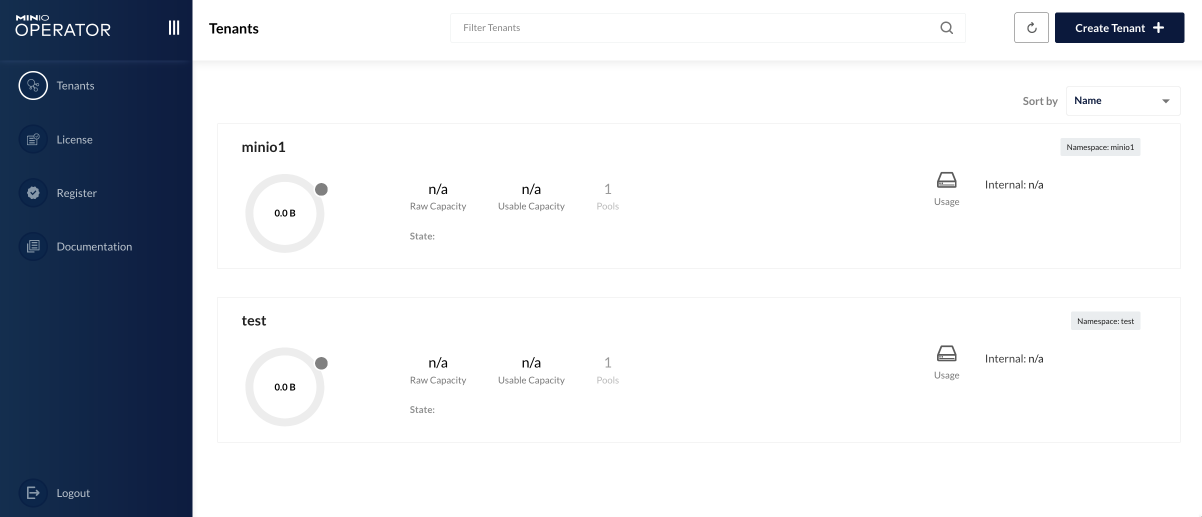
Click the + Create Tenant to start creating a MinIO Tenant.
2) Complete the Encryption Section
Reference the Deploy a MinIO Tenant procedure for complete documentation of other Tenant settings.
To enable SSE with a supported KMS target during Tenant deployment, select the Encryption section and toggle the switch to Enabled. You can then select the Radio button for the chosen KMS provider to display configuration settings for that provider.
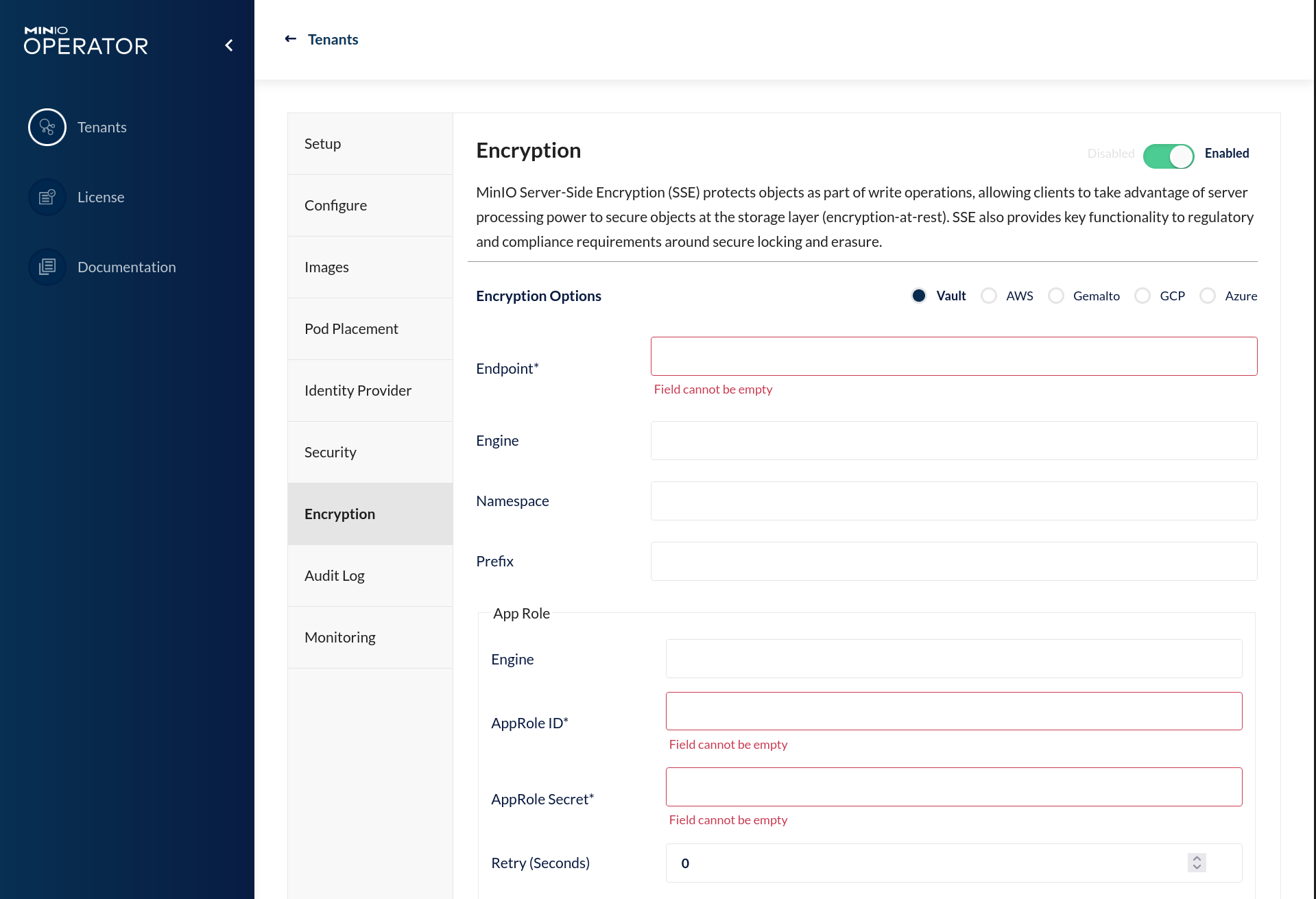
An asterisk * marks required fields.
Refer to the Configuration References section of the tutorial for your chosen supported KMS target for more information on the configuration options for your KMS.
Once you have completed the configuration, you can finish any remaining sections of Tenant Deployment.
3) Generate a New Encryption Key
Unseal Vault Before Creating Key
If required by your chosen provider, you must unseal the backing vault instance before creating new encryption keys. See the documentation for your chosen KMS solution for more information.
MinIO requires that the EK for a given bucket or object exist on the root KMS before performing SSE operations using that key.
You can use the mc admin kms key create command against the MinIO Tenant.
You must ensure your local host can access the MinIO Tenant pods and services before using mc to manage the Tenant.
For hosts internal to the Kubernetes cluster, you can use the service DNS name.
For hosts external to the Kubernetes cluster, specify the hostname of the service exposed by Ingress, Load Balancer, or similar Kubernetes network control component.
Run this command in a separate Terminal or Shell:
# Replace '-n minio' with the namespace of the MinIO deployment
# If you deployed the Tenant without TLS you may need to change the port range
# You can validate the ports in use by running
# kubectl get svc/minio -n minio
kubectl port forward svc/minio 443:443 -n minio
The following commands in a new Terminal or Shell window:
Connect a local
mcclient to the Tenant.Create the encryption key.
See Quickstart for instructions on installing mc on your local host.
# Replace USERNAME and PASSWORD with a user on the tenant with administrative permissions
# such as the root user
mc alias add k8s https://localhost:443 ROOTUSER ROOTPASSWORD
# Replace my-new-key with the name of the key you want to use for SSE-KMS
mc admin kms key create k8s encrypted-bucket-key
4) Enable SSE-KMS for a Bucket
You can use either the MinIO Tenant Console or the MinIO mc CLI to enable bucket-default SSE-KMS with the generated key:
Connect to the MinIO Tenant Console service and log in. For clients internal to the Kubernetes cluster, you can specify the service DNS name. For clients external to the Kubernetes cluster, specify the hostname of the service exposed by Ingress, Load Balancer, or similar Kubernetes network control component.
Once logged in, create a new Bucket and name it to your preference. Select the Gear icon to open the management view.
Select the pencil icon next to the Encryption field to open the modal for configuring a bucket default SSE scheme.
Select SSE-KMS, then enter the name of the key created in the previous step.
Once you save your changes, try to upload a file to the bucket. When viewing that file in the object browser, note that in the sidebar the metadata includes the SSE encryption scheme and information on the key used to encrypt that object. This indicates the successful encrypted state of the object.
Use the MinIO API Service to create a new alias for the MinIO deployment.
You can then use the mc encrypt set command to enable SSE-KMS encryption for a bucket:
mc alias set k8s https://minio.minio-tenant-1.svc.cluster-domain.example:443 ROOTUSER ROOTPASSWORD
mc mb k8s/encryptedbucket
mc encrypt set SSE-KMS encrypted-bucket-key k8s/encryptedbucket
For clients external to the Kubernetes cluster, specify the hostname of the service exposed by Ingress, Load Balancer, or similar Kubernetes network control component.
Write a file to the bucket using mc cp or any S3-compatible SDK with a PutObject function.
You can then run mc stat on the file to confirm the associated encryption metadata.